Preamble
Before extracting the data, we carry out a pre-diagnosis in order to know the complexity of the case and make a precise estimate. The unit may need to be opened and cleaned if necessary. Before any manipulation, we systematically take high resolution photos of the equipment received in order to avoid any complaints with our customers or with the transporters. An external and possibly internal visual inspection is then carried out.

Visual pre-diagnosis
We use several methods to recover data from a mobile device, either using conventional techniques or those developed in-house by our own research and development laboratory. We pay the utmost attention to your equipment so as not to damage your data. We therefore carry out most of our operations in an environment protected against electrostatic discharges as well as respecting the strictest standards of security and confidentiality.
Logic extraction

Even if access to the data sometimes requires substantial and costly resources, it may be enough to make minor repairs such as changing the screen, connectors or ribbon connectors to access it. Using state-of-the-art hardware and software, used in the world of law enforcement evidence search and data forensics, we are able to connect to thousands of device models and retrieve their data directly without disassembly.
Physical extraction
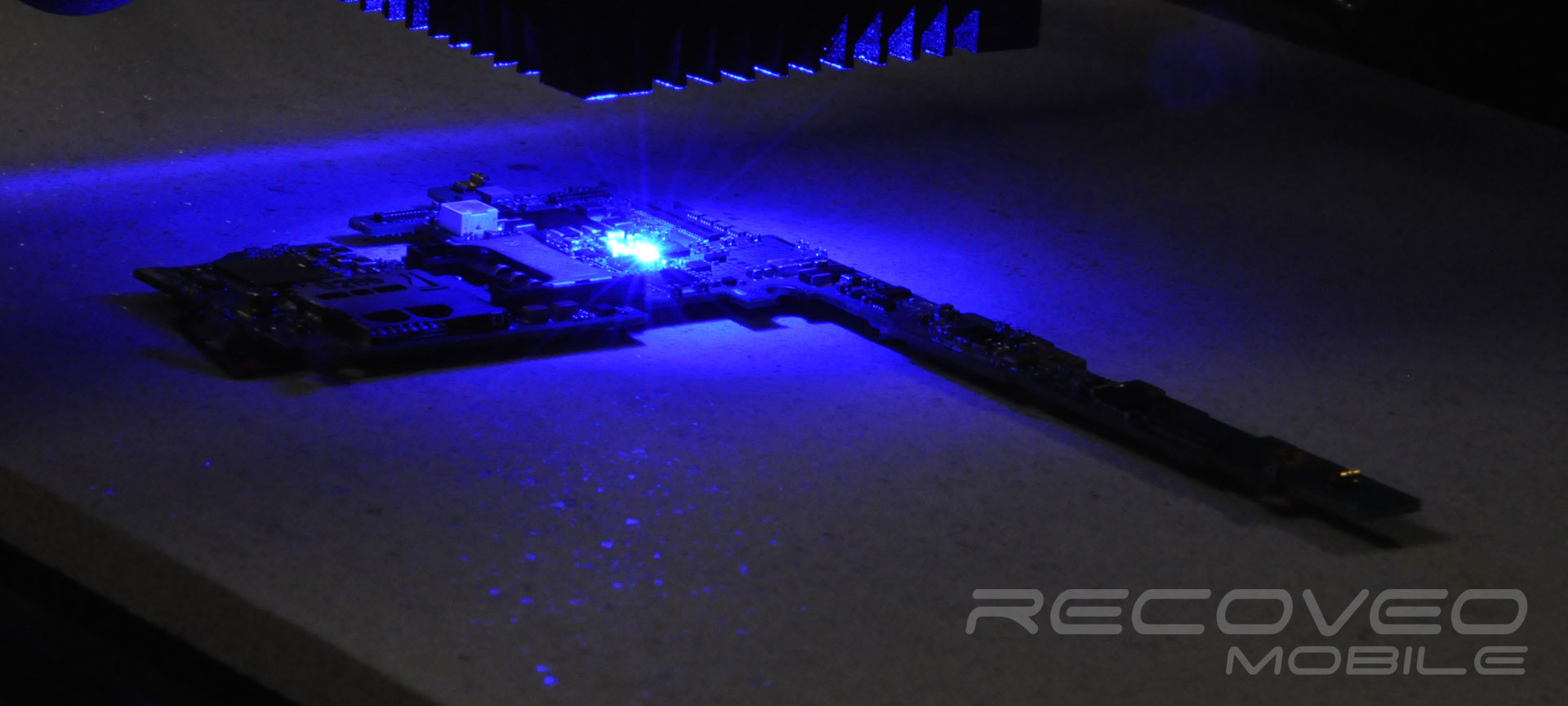
Cold Chip-Off
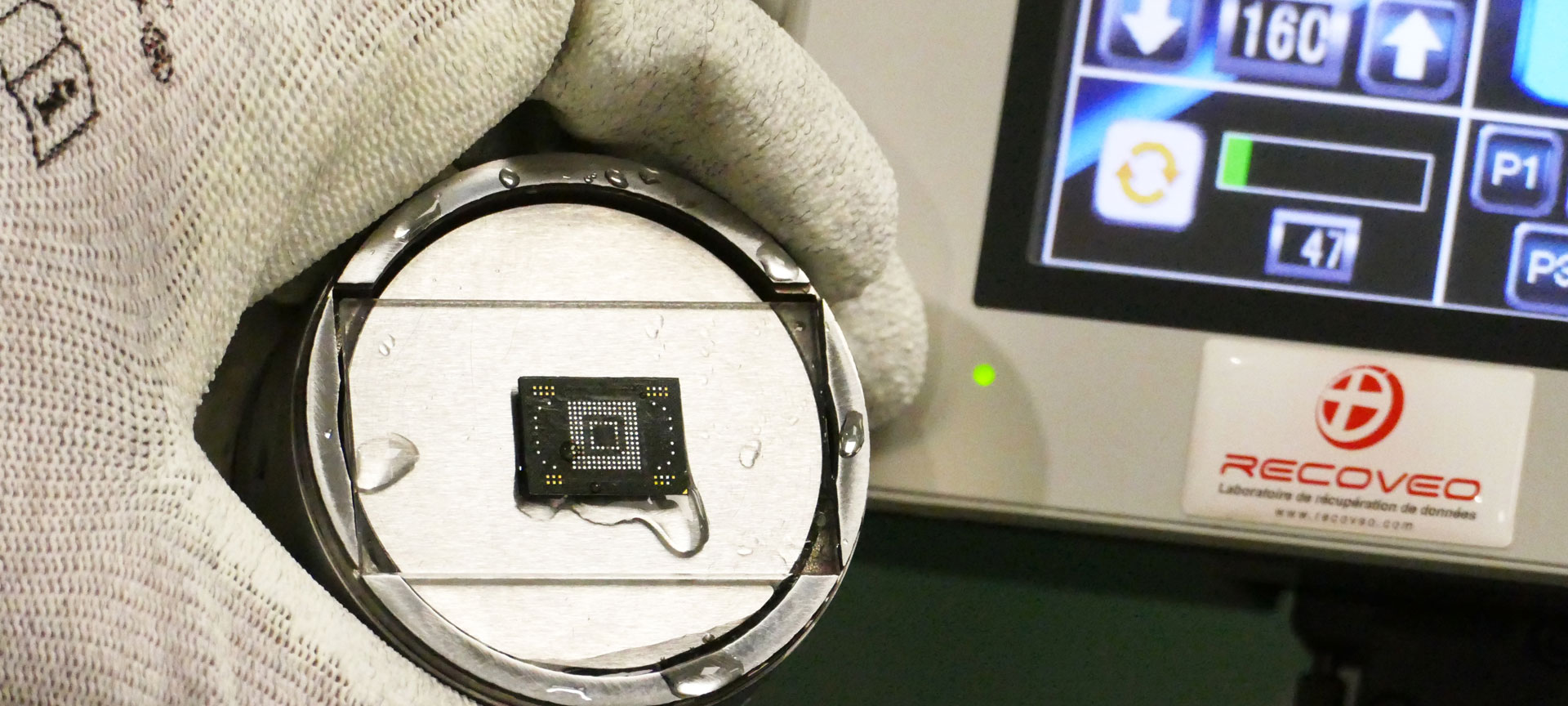
We may need to use the "Cold Chip-off", which involves removing the memory chip containing the data from the phone card or tablet and then reading the data directly from it. We are among the first companies in the world to use this unique process that guarantees the integrity of memory chips by avoiding heating them by desoldering them. We are Training Centre for other companies on this type of process and we market this type of equipment. This technique is said to be destructive for the equipment, because the electronic board where the memory is located is cut out with a precision laser.
Advanced methods
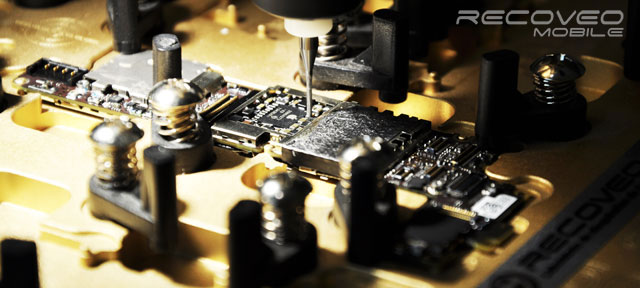
On certain equipment, in particular those where the data is encrypted and any form of access to it is otherwise impossible, we repair the motherboards or electronic circuits in such a way as to make them provisionally functional.
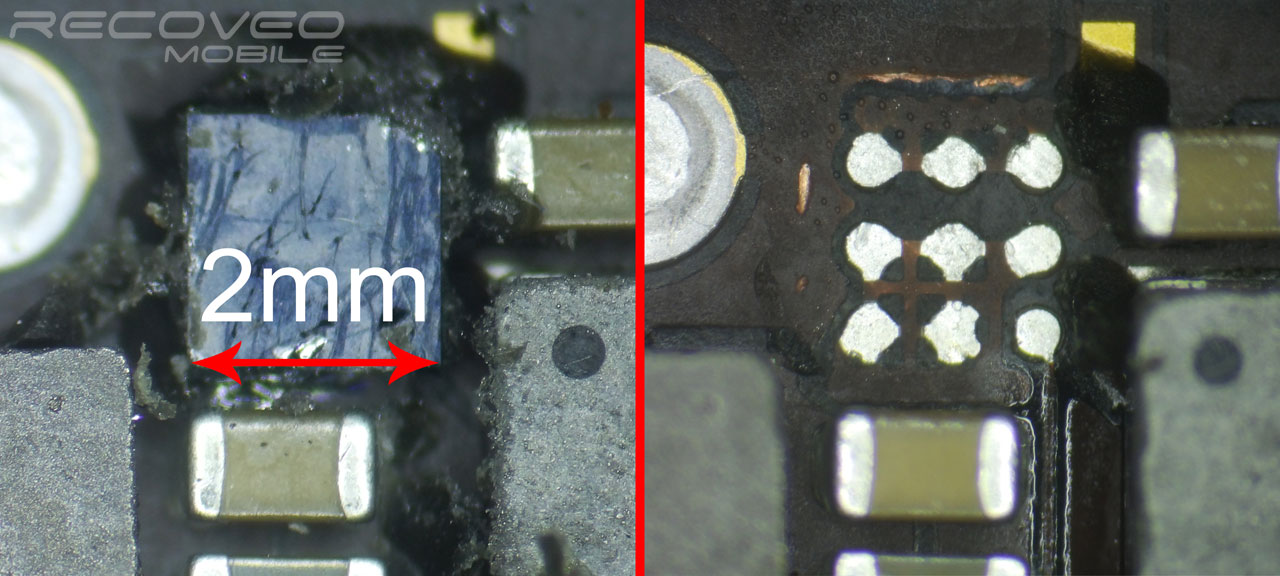
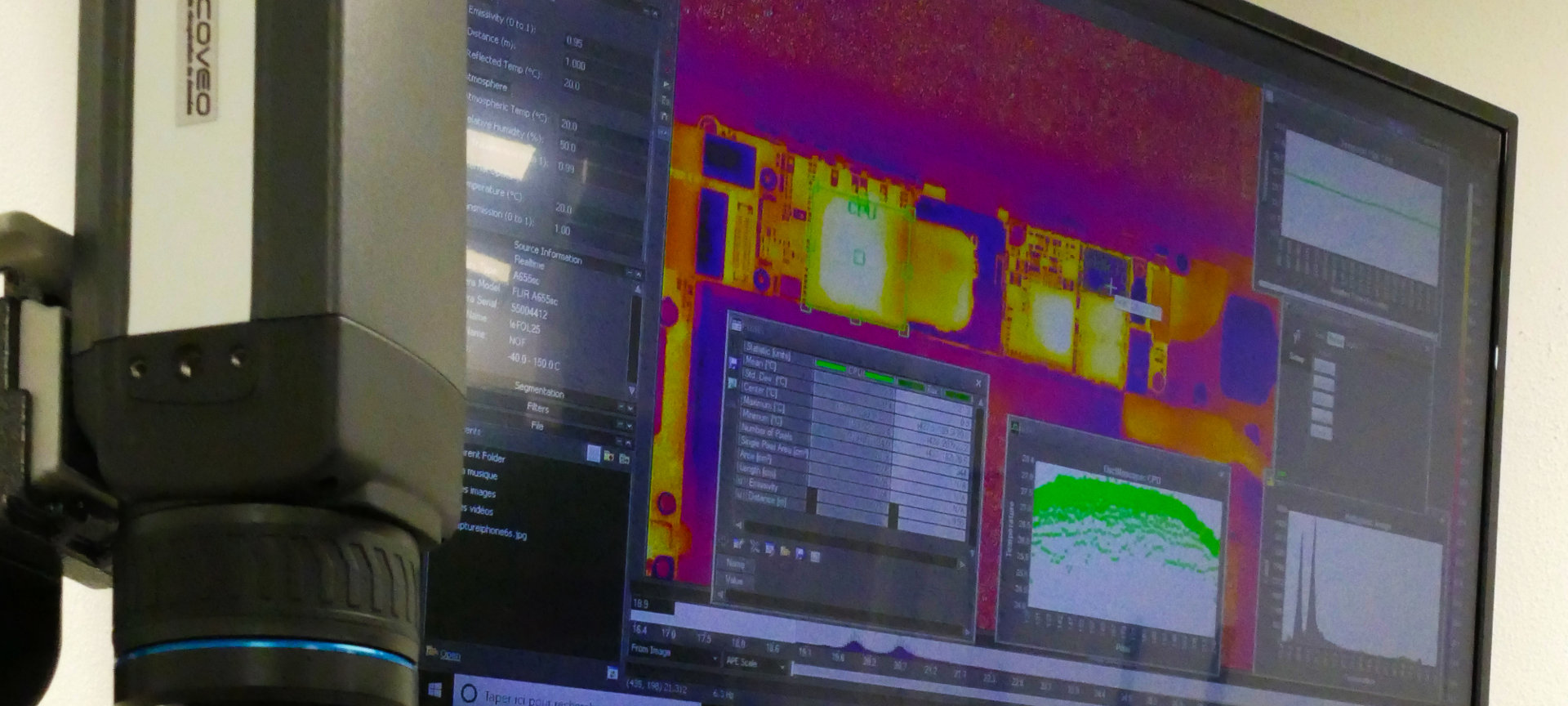
We use high-tech techniques and equipment to diagnose and repair: we are capable of reconstructing tracks and soldering with 25µm wires, we use 3D microscopy equipment, high-definition thermal microscopy and acoustic microscopy to obtain the most accurate diagnoses.
In the most extreme cases, when no more repairs are possible or conceivable, we are able to swap critical components (related to data or encryption) on another functional card. This technique is only used in extreme cases, when the electronic card of an iPhone is broken, for example.
Some techniques such as grinding (machining components with a precision CNC milling machine) or deoxidation of damaged cards are carried out with equipment and chemicals developed by our own R&D laboratory. This allows us to respond to specific problems. We free ourselves from the constraints imposed by existing tools or products on the market and we go much further in recovering your data.
Our technology allows us to take over cases that have been treated and not solved by other repairers: we make every effort to try to recover the equipment's data.
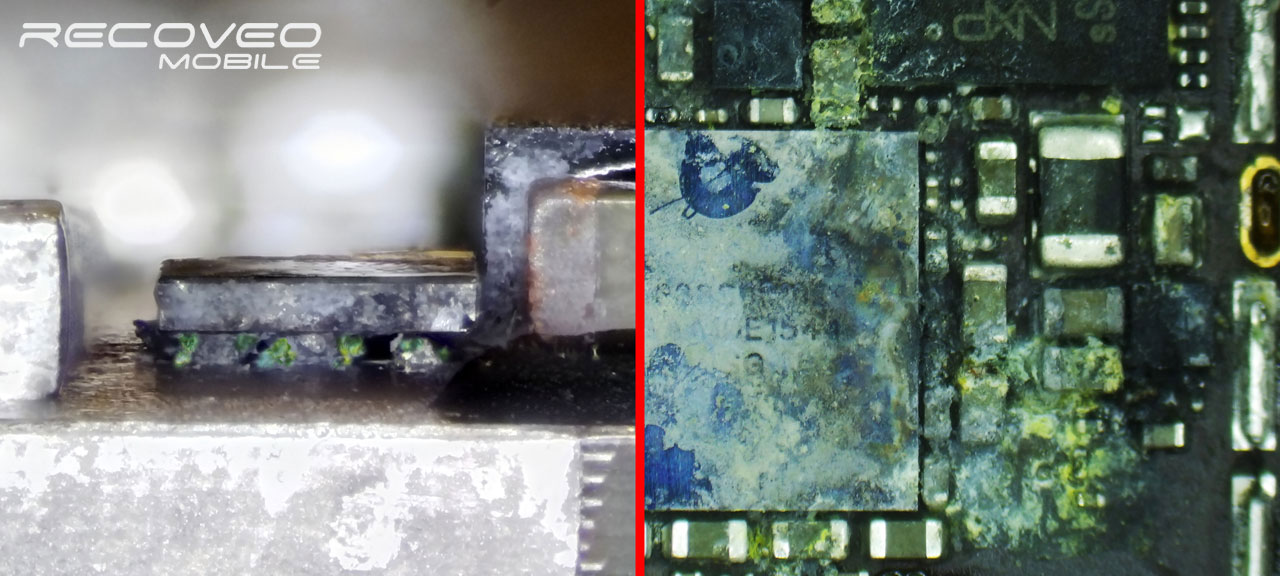
Oxydized component